Confidential Computing: How Encrypted Processing is Transforming Cloud Security
- Shiksha ROY

- Jun 2, 2025
- 4 min read
SHIKSHA ROY | DATE: JANUARY 29, 2025

In today's digital landscape, the cloud has become an indispensable tool for businesses, offering unparalleled flexibility, scalability, and cost-efficiency. However, as more sensitive data is migrated to the cloud, ensuring its security has become a paramount concern. Traditional security measures, while robust, often fall short in protecting data during processing. This is where confidential computing steps in, revolutionizing cloud security by keeping data encrypted even while it is being processed. By leveraging advanced technologies like Trusted Execution Environments (TEEs) and encrypted processing, confidential computing provides a new layer of security that addresses the vulnerabilities of data in use. This transformative approach not only enhances data privacy and security but also opens up new possibilities for secure data collaboration and innovation across various industries.
What is Confidential Computing?
Confidential computing is a security model that ensures data remains encrypted not only when stored or transmitted but also while being processed in memory. It utilizes Trusted Execution Environments (TEEs)—secure enclaves within processors—that isolate data from unauthorized access, including from the cloud provider and system administrators.
Key Components of Confidential Computing
Trusted Execution Environments (TEEs): TEEs are secure areas within a CPU that protect data during processing. They prevent unauthorized access or modification of applications and data while they are in use. TEEs ensure data confidentiality, integrity, and code integrity, making them a cornerstone of confidential computing.
Remote Attestation: Remote attestation is a process that verifies the trustworthiness of a TEE before sensitive data is processed. It ensures that the TEE is genuine and operating with an acceptable security posture. This verification process is crucial for maintaining the integrity of confidential computing environments.
Encrypted Processing: Encrypted processing involves performing computations on encrypted data within TEEs. This ensures that data remains protected from unauthorized access, even during processing. The encryption keys are managed securely, and any attempt to access them by unauthorized code results in the cancellation of the computation.
How Confidential Computing Enhances Cloud Security
Cloud environments introduce unique security risks, including insider threats, multi-tenancy vulnerabilities, and external cyberattacks. Confidential computing mitigates these risks by leveraging encrypted processing. Below are some of its transformative impacts on cloud security:
Data Privacy and Confidentiality
Confidential computing ensures that even cloud providers cannot access the data being processed. This is particularly critical for industries like healthcare, finance, and government, where privacy regulations require strict data protection measures.

Secure Multi-Tenant Environments
In cloud computing, multiple organizations share the same physical infrastructure. Confidential computing prevents unauthorized access between tenants, ensuring that data remains isolated and protected from potential breaches.
Protection Against Insider Threats
System administrators and cloud providers traditionally have elevated privileges that could be misused. With confidential computing, even those with administrative access cannot view or manipulate encrypted data, reducing the risk of insider threats.
Regulatory Compliance and Data Sovereignty
Regulations like GDPR, HIPAA, and CCPA demand strict data protection and privacy controls. Confidential computing helps organizations comply with these standards by ensuring that sensitive data remains encrypted during processing, meeting stringent compliance requirements.
Enhancing Secure AI and Machine Learning
Confidential computing enables secure data sharing and processing for AI and machine learning applications. Organizations can train AI models on sensitive datasets without exposing underlying data, fostering secure collaborations between companies.
Benefits of Confidential Computing
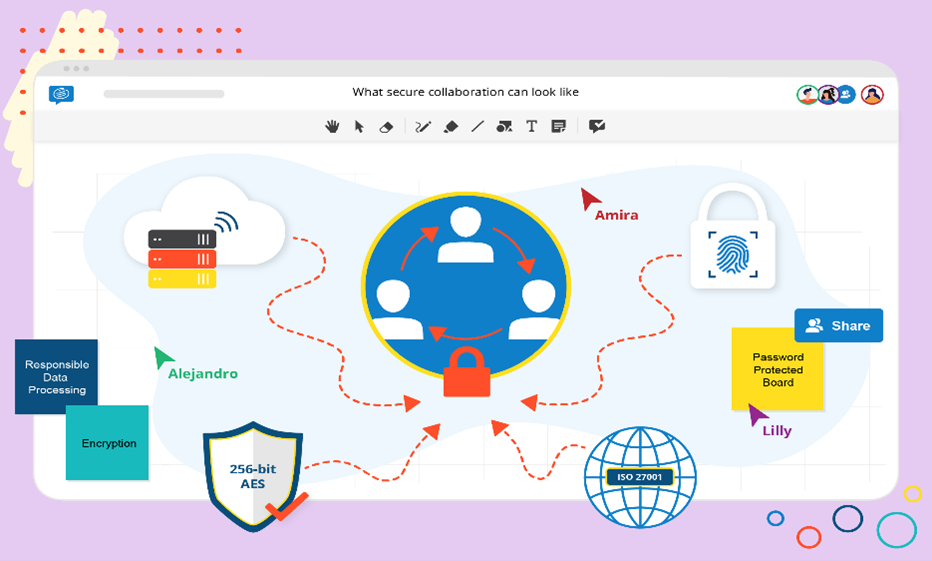
Secure Data Collaboration
By enabling encrypted processing, confidential computing allows multiple parties to collaborate on data analysis without exposing the actual data. This is beneficial for sectors like research and development, where data sharing is essential.
Enhanced Data Privacy
Confidential computing ensures that sensitive data remains encrypted throughout its lifecycle, significantly enhancing data privacy. This is particularly important for industries handling highly sensitive information, such as healthcare and finance.
Improved Cloud Security
Confidential computing addresses the last remaining vulnerability in cloud security by protecting data in use. This provides businesses with greater confidence to move sensitive workloads to the cloud, knowing that their data is secure at all stages.
Use Cases of Confidential Computing
Healthcare
In healthcare, confidential computing can protect patient data during processing, ensuring compliance with regulations like HIPAA. It enables secure data sharing for research and treatment without compromising patient privacy3.
Financial Services
Financial institutions can use confidential computing to secure transactions and sensitive financial data. This technology helps in maintaining the confidentiality and integrity of financial operations, reducing the risk of data breaches.
Artificial Intelligence and Machine Learning
Confidential computing allows AI and ML models to be trained on encrypted data, preserving data privacy. This is crucial for industries that rely on sensitive data for developing predictive models.
Future of Confidential Computing

As cloud adoption continues to grow, confidential computing is expected to become a standard security practice. Innovations in hardware security, cryptographic techniques, and software integration will further enhance its efficiency and scalability. With organizations prioritizing data privacy, confidential computing will play a pivotal role in shaping the future of cloud security.
Conclusion
Confidential computing is transforming cloud security by ensuring data remains encrypted during processing. With its ability to protect data at all stages, it offers enhanced privacy, secure collaboration, and improved cloud security. As businesses continue to adopt cloud services, confidential computing will play a pivotal role in safeguarding sensitive information and maintaining trust in digital environments.
Citations
Wikipedia contributors. (2025, January 20). Confidential computing. Wikipedia. https://en.wikipedia.org/wiki/Confidential_computing
Goud, N. (2024, September 17). Exploring the essence of confidential computing - cybersecurity insiders. Cybersecurity Insiders. https://www.cybersecurity-insiders.com/exploring-the-essence-of-confidential-computing/
Image Citations
Multi-Tenant architecture for cloud Apps - Benefits & types. (n.d.). ThinkSys Inc. https://thinksys.com/cloud/multi-tenant-architecture-cloud-apps/
Mirjam. (2024, April 23). 4 features of a secure collaboration tool | ConceptBoard. Conceptboard. https://conceptboard.com/blog/secure-collaboration-tool-features/
Simplilearn. (2023, September 20). Cryptography Demystified: Protecting your digital privacy. Simplilearn.com. https://www.simplilearn.com/tutorials/cryptography-tutorial/what-is-cryptography





Comments