Cybersecurity in Manufacturing: Safeguarding the Backbone of Industry
- Arpita (BISWAS) MAJUMDAR

- Jun 24, 2025
- 4 min read
Updated: Jul 9, 2025
ARPITA (BISWAS) MAJUMDER | DATE: MAY 27, 2024

In today’s era of rapid industrial growth, where digital transformation is the norm, cybersecurity in manufacturing is as vital as traditional physical security. The industry’s adoption of interconnected technologies, especially with operational technology (OT) merging with information technology (IT), has introduced new opportunities but also increased vulnerabilities. As factories become "smart" and rely heavily on networked systems, they open themselves to cyber threats that could jeopardize production, intellectual property, and sensitive data. The stakes are high, and so is the urgency for cybersecurity in manufacturing.
The Escalating Cyber Threats Facing Manufacturers
Manufacturing has experienced numerous high-profile cyber breaches in recent years. For instance:
Boeing faced a significant breach in 2019 that led to the exposure of sensitive aircraft designs, resulting in a loss of over $300 million. Tesla had its operations disrupted in 2020 due to a ransomware attack that cost approximately $150 million. Honda encountered a similar attack in 2021, with its production line and communication systems impacted, resulting in losses around $200 million. Intel suffered a data leak in 2023, exposing critical semiconductor design files and incurring losses estimated at $250 million. These incidents underline how complex and varied the threats are. Attackers are more sophisticated than ever, often targeting essential infrastructure and capitalizing on gaps in cybersecurity.
Unique Cybersecurity Hurdles Across Manufacturing Sectors
Each manufacturing sector grapples with its own cybersecurity needs and challenges:
Automotive Manufacturing
Protecting vehicle-to-vehicle communication systems, proprietary designs, and supply chains is essential. Moreover, as the automotive industry leans toward connected and autonomous vehicles, securing this infrastructure becomes critical.
Aerospace and Defense
This sector manages some of the most sensitive information and must enforce rigorous access controls across global supply chains. Compliance with stringent industry regulations, such as ITAR (International Traffic in Arms Regulations), adds an extra layer of complexity.
Chemical and Pharmaceutical
Protecting intellectual property, like proprietary formulas and research data, is a major priority, as is securing SCADA (Supervisory Control and Data Acquisition) systems and industrial control networks.
Electronics and Computer Manufacturing
For manufacturers producing semiconductors or computer hardware, safeguarding intellectual property throughout the lifecycle is paramount. Ensuring a secure and resilient supply chain is also crucial in this sector.
Core Cybersecurity Strategies for a Resilient Manufacturing Sector
The evolving cyber threat landscape calls for a robust cybersecurity framework, which should include several foundational strategies:
Network Segmentation
Dividing OT and IT networks minimizes the risk of cross-infection from cyber threats and helps contain attacks, preventing them from spreading throughout the organization.
Access Controls
Role-based access control, combined with multi-factor authentication, ensures that only authorized individuals can access sensitive systems. Regular reviews of access permissions can further enhance security.
Endpoint Security
With a vast network of IoT and IIoT devices in manufacturing, endpoint security becomes indispensable. This involves patch management, real-time monitoring, and frequent updates to secure connected devices.
Continuous Monitoring
Real-time detection tools help manufacturers swiftly identify and respond to cyber threats, reducing downtime and mitigating the risk of prolonged operational impacts.
Regulatory Compliance Frameworks
Manufacturers must navigate a complex web of regulatory requirements, including:
NIST SP 800-171 to protect Controlled Unclassified Information (CUI).
CMMC for Department of Defense contractors.
GDPR for manufacturers handling EU citizen data.
ISO/IEC 27001 as a global standard for information security.
HIPAA for medical device manufacturers.
Best Practices to Fortify Manufacturing Cybersecurity
To bolster defenses against an array of cyber threats, manufacturers can employ these key best practices:

Adopt a Zero Trust Architecture
Zero Trust assumes no one can be trusted by default. Every device and user must be verified before gaining access. Continuous verification at all access points adds another layer of security.
Strengthen Network Security
Advanced firewalls and intrusion detection systems (IDS) are crucial for protecting networks. Regular security audits and penetration tests can help identify and address vulnerabilities.
Secure IoT Devices
Manufacturers must keep IoT devices updated and isolate them within segmented networks to prevent potential compromise.
Employee Training
Educating employees about cybersecurity is vital. Training them to recognize phishing attacks and social engineering can help prevent breaches originating from human error.
Incident Response Planning
A well-prepared incident response plan should outline clear communication protocols. Regular drills can improve response times and minimize potential damage during real incidents.
The Road Ahead: Adapting to a Digitally Transformed World
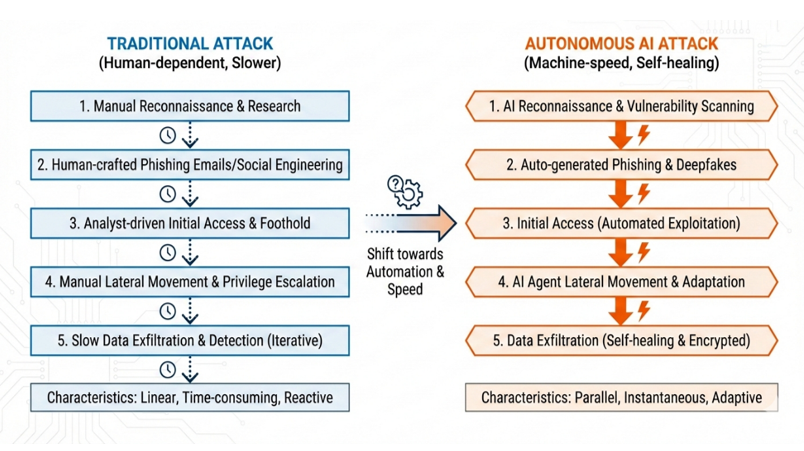
With the ongoing integration of artificial intelligence (AI) and machine learning (ML) into manufacturing, the cybersecurity landscape will continue to evolve. AI-powered threat detection can identify patterns and respond to threats faster than traditional methods, which will be indispensable in safeguarding the industry's future. By investing in strong cybersecurity frameworks and implementing rigorous protocols, manufacturers can not only protect their operations and data but also ensure the resilience and reliability of the industrial systems that form the backbone of modern society.
Citations:
Manufacturing Cyber Security: A Comprehensive Guide | Mission Secure. (n.d.). https://www.missionsecure.com/manufacturing-cyber-security
Cybersecurity for smart factories. (n.d.). Deloitte United States. https://www2.deloitte.com/us/en/pages/energy-and-resources/articles/smart-factory-cybersecurity-manufacturing-industry.html
Sectrio. (2024, May 31). Cybersecurity compliance for Manufacturers | A complete guide. Sectrio. https://sectrio.com/blog/cybersecurity-compliance-in-manufacturing-guide/
Cybersecurity in the manufacturing industry | UpGuard. (n.d.). https://www.upguard.com/blog/cybersecurity-in-the-manufacturing-industry
Gordon, J. (2024, January 9). Manufacturing Cybersecurity – standards, regulation and compliance. Industrial Cyber. https://industrialcyber.co/expert/manufacturing-cybersecurity-standards-regulation-and-compliance/
Databricks. (2024, July 11). Cybersecurity in Manufacturing | DataBricks blog. https://www.databricks.com/blog/2023/03/01/cybersecurity-manufacturing.html
Cyber security in smart Factories: 7 Tips for Securing your Operations - Atlas Copco. (n.d.). Atlas Copco. https://www.atlascopco.com/en-uk/itba/expert-hub/articles/cyber-secutiry-in-smart-factories
Image Sources
3,051 Manufacturing Cyber security images, stock photos, and vectors | Shutterstock. (n.d.). Shutterstock. https://www.shutterstock.com/search/manufacturing-cyber-security
Alqudhaibi, A., Albarrak, M., Jagtap, S., Williams, N., & Salonitis, K. (2024). Securing industry 4.0: Assessing cybersecurity challenges and proposing strategies for manufacturing management. Cyber Security and Applications, 3, 100067. https://doi.org/10.1016/j.csa.2024.100067
Common cyber security threats in manufacturing industry | Briskinfosec. (n.d.). https://www.briskinfosec.com/blogs/blogsdetail/Common-Cyber-Security-Threats-In-Manufacturing-Industry
About the Author
Arpita (Biswas) Majumder is a key member of the CEO's Office at QBA USA, the parent company of AmeriSOURCE, where she also contributes to the digital marketing team. With a master’s degree in environmental science, she brings valuable insights into a wide range of cutting-edge technological areas and enjoys writing blog posts and whitepapers. Recognized for her tireless commitment, Arpita consistently delivers exceptional support to the CEO and to team members.




Comments