The Ethics of Hacking: When Is Ethical Hacking Truly Ethical?
- Shilpi Mondal

- May 22, 2025
- 4 min read
SHILPI MONDAL| DATE: MARCH 18,2025

Introduction
In today's digital landscape, hacking often conjures images of malicious actors exploiting system vulnerabilities for personal gain. However, ethical hacking, also known as penetration testing or white-hat hacking, involves authorized professionals identifying and addressing security weaknesses to fortify systems against potential threats. This practice is essential for organizations aiming to protect their digital assets. Yet, the ethicality of ethical hacking hinges on adherence to specific principles and guidelines. This article delves into the criteria that define truly ethical hacking and explores real-world scenarios that highlight its significance.
Defining Ethical Hacking

Ethical hacking entails the deliberate and authorized probing of computer systems, networks, or applications to uncover vulnerabilities that could be exploited by malicious entities. Unlike black-hat hackers who operate illegally, ethical hackers perform their assessments with the explicit consent of the system owners, aiming to enhance security measures. Their primary objectives include:
Identifying Security Flaws: Detecting vulnerabilities before malicious hackers can exploit them.
Assessing Security Posture: Evaluating the effectiveness of existing security protocols and controls.
Ensuring Compliance: Verifying adherence to industry standards and regulatory requirements.
Preventing Unauthorized Access: Implementing measures to safeguard sensitive data and systems.
By simulating potential attack vectors, ethical hackers provide organizations with invaluable insights into their security landscapes, enabling proactive defense strategies.
Core Principles of Ethical Hacking
For hacking activities to be deemed ethical, they must align with the following foundational principles:
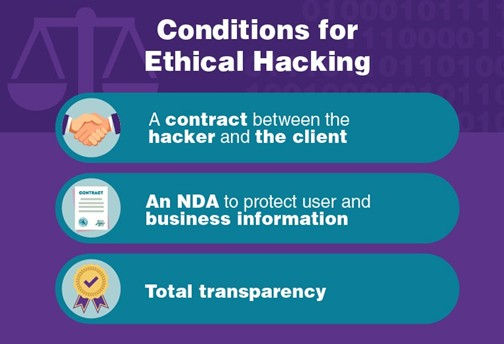
Explicit Authorization: Ethical hackers must obtain clear and documented permission from the system owner before initiating any testing. This authorization ensures that all activities are legally sanctioned and transparent.
Integrity and Confidentiality: Maintaining the confidentiality of the organization's data is paramount. Ethical hackers are entrusted with sensitive information and must handle it with the utmost integrity, ensuring that findings are disclosed only to authorized personnel.
Transparency and Reporting: All discovered vulnerabilities should be promptly and thoroughly reported to the organization, accompanied by actionable recommendations for remediation. This transparency fosters trust and facilitates effective risk management.
Legal Compliance: Ethical hackers must operate within the bounds of applicable laws and regulations, avoiding any actions that could be construed as malicious or unauthorized.
Minimization of Harm: Testing should be conducted in a manner that avoids causing any harm to the system, its data, or its users. Ethical hackers should employ methods that minimize potential disruptions or
damages.
Case Studies Illustrating Ethical Hacking
Real-world examples underscore the critical role of ethical hacking in safeguarding digital infrastructures:
Visa Contactless Card Vulnerability: In 2019, security researchers identified a flaw in Visa's contactless payment system that allowed transactions to bypass payment limits without authorization. By responsibly disclosing this vulnerability, they enabled Visa to address the issue before it could be exploited maliciously.

Internal Network Penetration Test: A security team conducted an internal network penetration test for a client, successfully taking control over the entire network. This proactive assessment helped the client secure their infrastructure against real-world cyber attacks.
Jadavpur University Website Security: In 2014, amidst student agitations, the website of Jadavpur University in India was hacked, causing a media sensation. The Indian School of Ethical Hacking intervened, analyzed the code, and stopped the relentless attacks, highlighting the importance of ethical hacking in protecting institutional digital assets.
Navigating Ethical Dilemmas
Despite clear guidelines, ethical hackers may encounter situations that challenge ethical boundaries:
Scope Creep: Expanding testing beyond the agreed-upon scope without explicit consent can lead to unauthorized access, breaching ethical and legal standards.
Dual-Use Knowledge: The skills and tools used in ethical hacking can also be employed for malicious purposes. Ethical hackers must exercise discretion and uphold professional integrity to prevent misuse.
Conflict of Interest: Engaging in activities that could benefit a competitor or personal interest at the expense of the client compromises ethical standards.
Conclusion
Ethical hacking serves as a cornerstone of modern cybersecurity, enabling organizations to proactively identify and mitigate vulnerabilities. However, the ethicality of such practices is contingent upon strict adherence to principles of authorization, integrity, transparency, legal compliance, and harm minimization. By upholding these standards, ethical hackers not only protect digital infrastructures but also reinforce the trust and reliability essential in today's interconnected world.
Citations:
EC-Council. (2024, December 24). Code Of Ethics | EC-Council. https://www.eccouncil.org/code-of-ethics/
G, J. (2021, December 23). The definitive guide to ethical hacking – My Computer Career. My Computer Career. https://www.mycomputercareer.edu/the-definitive-guide-to-ethical-hacking/
Sharma, V. (2022, July 13). Ethical Hacking case Study: Times when hackers avoided setbacks. Knowledge hut. https://www.knowledgehut.com/blog/security/ethical-hacking-case-study
Case studies | ISOAH-CORPORATE | Our services | Indian School of Ethical Hacking | IT Security Company in Kolkata, India. (n.d.). https://www.isoah.com/case-studies.php
Case studies – Cyber Threat Defense. (n.d.). https://ctdefense.com/case-studies/
Image Citations:
What is Ethical Hacking? - Logsign. (n.d.). Logsign. https://www.logsign.com/blog/what-is-ethical-hacking/
Human, H. (2024, August 19). The Ultimate Guide to Ethical Hacking | What You Need to Know in 2025. vpnMentor. https://www.vpnmentor.com/blog/ultimate-guide-to-ethical-hacking/
Sorial, M. (2024, May 1). 6 Case studies of Ethical Hacking: Cyber disasters prevented. Internet Safety Statistics. https://www.internetsafetystatistics.com/case-studies-ethical-hacking/





Comments